OUR TECHNOLOGY Contactless Palm Verification
A privacy-centric biometric alternative for seamless, secure verification
Download one-pagerPioneering technology delivering secure and private biometric verification and identification
Contact usEvery palm is as unique as a fingerprint, making it incredibly reliable. Utilizing it in biometric recognition puts privacy first by eliminating the need for facial images or linking data to personal identifiers. A simple palm gesture gives users complete control over their security.
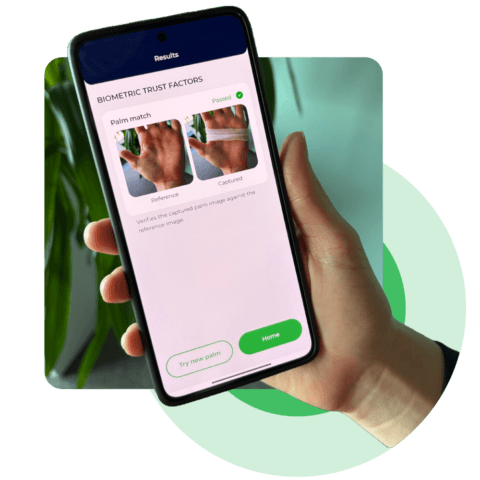
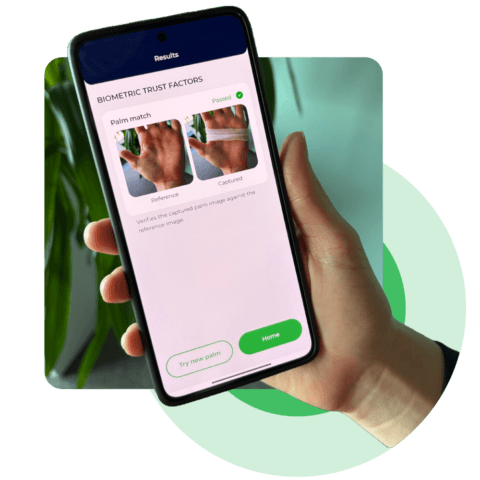
Contactless palm verification adds a secure, fast, and frictionless second factor to remote identity verification. A simple palm gesture reassures that the verified face matches the genuine user.
Our palm verification provides a secure, contactless layer of biometric verification to strengthen two-factor authentication (2FA) processes. Palm verification can also make a secure alternative to face verification, offering users privacy and control over
their security.
Indoors or outdoors, from new to older phones, it performs consistently. Unlike vein scanning, its accuracy stays unaffected by temperature or health factors. The algorithm is trained on a diverse dataset, ensuring consistent accuracy across all skin tones, tolerating scars or aging.
Advanced liveness detection protects against
presentation attacks, such as printed or screen images. Our video injection detection further safeguards against deepfakes and digital manipulation, ensuring
the image always comes from a genuine camera.
Our palm verification integrates easily into any
digital onboarding or authentication workflow. It
supports both on-premise and cloud deployment, can be tuned for high-security or user-centric use cases, and scales effortlessly across platforms and devices.
Because contactless palm recognition works with everyday devices like smartphones or IP cameras, there’s no need for specialized equipment. This makes contactless palm recognition deployment fast, simple, and accessible for a wide range of uses.
Palm recognition provides a secure, contactless layer of biometric verification to strengthen 2FA processes.
Users can reset passwords securely by verifying their identity with a unique palm scan.
A palm scan gives users instant and contactless access, foregoing the need for passwords.
Palm scans act as a human-verification step, preventing automated attacks while ensuring user convenience and privacy.
Enable medical staff to authenticate patient records quickly and hygienically, keeping sensitive data safe.
Match a user’s selfie with their identity document face portrait using industry- leading facial biometric algorithms.
Users can authorize transactions with a simple palm scan for hassle-free purchases.
Passengers can board faster without fumbling for tickets or cards.
Palm recognition outperforms other biometric methods in accuracy, thanks to the unique details captured in palmprints. With an extremely low False Match Rate (FMR), it is one of the most secure solutions available today. It works reliably even when some parts of the palm are covered.
The process is intuitive – a user simply holds their hand up to the camera. Our system handles the rest, capturing and analyzing the image in moments. Both contactless palm verification and identification are fast and accurate and do not require any extra hardware or complex setups.
Contactless palm verification does not require linking to facial data or ID cards. Images of palms are rarely shared publicly, and the act of showing one’s palm is intentional, signaling consent.
This approach is ideal for privacy-centric applications. It minimizes the risk of data misuse, meets stringent privacy regulations, and offers a better alternative for those unable or unwilling to use facial recognition due to cultural, personal, or situational preferences.


With contactless palm identification, a simple wave of the hand in front of a camera grants entry without the hassle of physical keys or cards.
Given its flexibility, it works seamlessly for users wearing head coverings or masks, as it doesn’t depend on facial data. Easily integrated into existing access systems, palm recognition can replace or complement other biometrics like fingerprints or facial scans.
Best of all, contactless palm identification prioritizes user privacy. The palm is enough as users do not need to provide personal identifiers like face photos or IDs to get access.


We use regular smartphone cameras to take pictures of the palm. This means we only use the light that is visible to the human eye. We then use the image of the palm itself for identification, instead of focusing on specific features like veins or the shape of the fingers.
We are taking only a visual image of the hand, so any health conditions do not have an effect on our method. It is also independent of the hand temperature.
Some parts of the palm can be covered, but the algorithm can still do matching.
The scanning of palms is easier compared to fingerprints as a lower resolution is sufficient (Fingerprints require at least 350 DPI resolution while 500 DPI is recommended). A resolution between 75-100 DPI will do for palm matching, so the hardware requirement is 5x less.
It does not affect the capture at all. A freezing cold hand can turn red in case of a light skin tone, but this does not affect the comparison algorithm either as it uses the contrasting features and not the color.
Most cameras used in smartphones should work. The camera has to support at least 800×600 resolution and should be able to focus at a distance of 30-40 centimeters. Most cameras, even those on 10-year-old smartphones, should work. Some cameras will struggle more in difficult conditions (e.g., low light), but in normal conditions, they work well. Furthermore, our toolkit supports notebook web cameras that are generally of lesser quality than smartphone cameras.
Yes, we also support identification. Contact us for more information.
A privacy-centric biometric alternative for seamless, secure verification
Download one-pager